AMD Quietly Lists 31 New CPU Vulnerabilities, Issues Patch Guidance
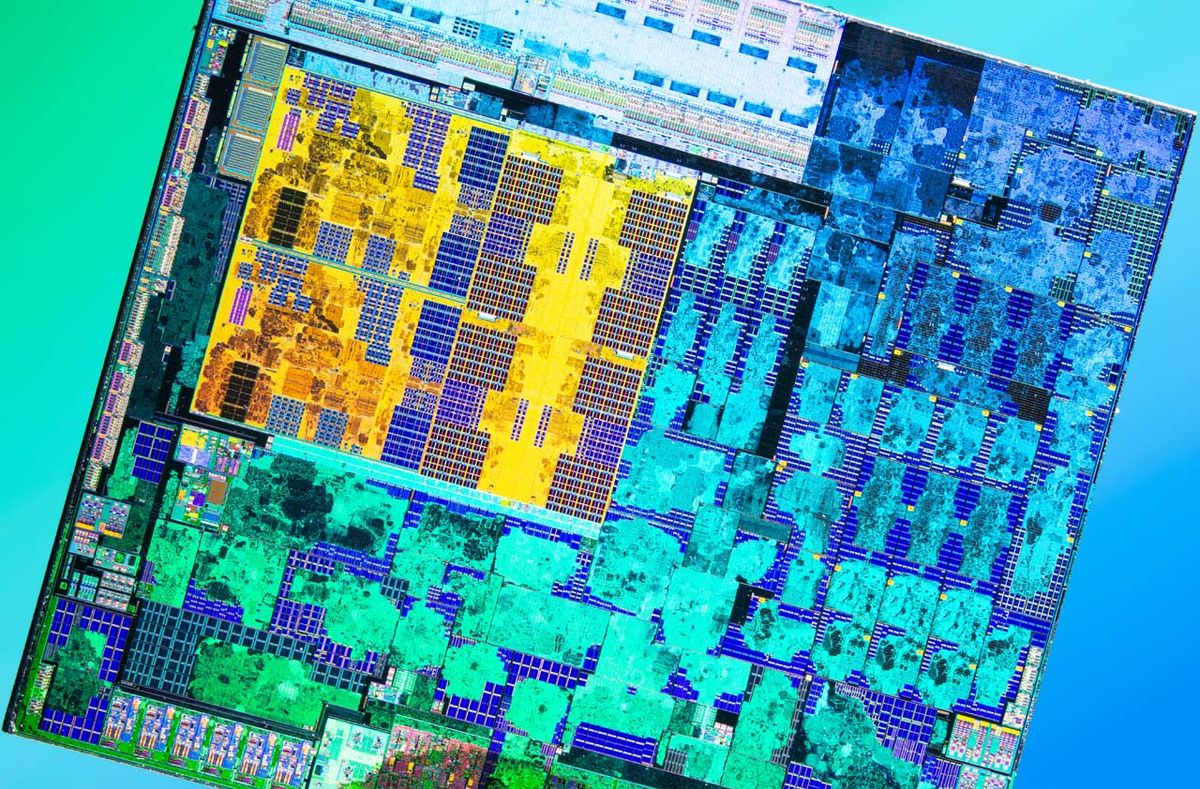
AMD quietly divulged 31 new CPU vulnerabilities in a January update, spanning its Ryzen chips for shoppers and the EPYC info centre processors. The vulnerability update also features a record of AGESA variations, with mitigations for the impacted processors. AMD discovered the vulnerabilities in a coordinated disclosure with many researchers, such as groups from Google, Apple and Oracle, which gave the corporation time to establish mitigations prior to the general public listings. On the other hand, AMD did not announce the vulnerabilities with a press release or other outreach — it merely posted the lists — so we’re performing to tease out the specifics and will update when we have additional details.
AMD has stated the several AGESA revisions it has issued to its OEMs to patch the vulnerabilities (AGESA code is employed to create BIOS/UEFI code). Nonetheless, the availability of new BIOS patches with the new AGESA code will fluctuate by vendor. That usually means you are going to have to look at with your motherboard or procedure vendor to see if it has posted new BIOS revisions with the right AGESA code.
AMD tells us that it typically challenges its vulnerability disclosures 2 times a year, in May perhaps and November, but chose to launch some in January due to the relatively big variety of new vulnerabilities and the timing of the mitigations. It just isn’t obvious nonetheless if there will be efficiency penalties as we have witnessed with other mitigations, like Spectre and Meltdown.
As we’ve noticed at instances with more mature techniques, some could possibly not be updated. It also seems that some impacted types don’t still have mitigations.
The vulnerabilities consist of three new variants for the buyer-geared Ryzen desktop Laptop, HEDT, Professional, and Mobile processors. One of the vulnerabilities is stated as high severity, even though the other two are rated as Medium or Minimal severity. These vulnerabilities can be exploited by means of both BIOS hacks or an attack on the AMD Protected Processor (ASP) bootloader.
The vulnerabilities span the Ryzen 2000-series Pinnacle Ridge desktop chips, alongside with the 2000- and 5000-sequence APU solution traces that appear with integrated graphics (Raven Ridge, Cezanne). In addition, AMD’s Threadripper 2000- and 3000-sequence HEDT and Pro processors are also impacted, together with quite a few Ryzen 2000-, 3000-, 5000-, 6000- and Athlon 3000-sequence mobile processors.
AMD has also outlined 28 vulnerabilities for its EPYC processors, four of which are large severity. 3 of the higher-severity variants enable arbitrary code execution by way of many attack vectors, even though a person will allow crafting facts to specific locations that can guide to decline of data integrity and availability. Researchers also unearthed 15 other vulnerabilities ranked as medium severity and nine low-severity vulnerabilities.
AMD’s chips have lengthy been identified for having less identified vulnerabilities than Intel’s products. Nevertheless, it can be really hard to verify if the originally limited discoveries in AMD processors were due to a protection-first approach to hardened processor structure, or if researchers and attackers simply concentrated on Intel’s processors because of to their commanding market share: Attackers virtually normally concentration on the broadest cross-area feasible.
As these, AMD’s modern achievement in clawing absent marketplace share from Intel, especially in the stability-concentrated info heart market, will locate researchers turning their eyes more towards AMD’s architectures in look for of opportunity safety gaps. AMD has also had quite a few other new vulnerability disclosures in the latest earlier, like a Meltdown-esque variant that requires program re-coding, together with Hertzbleed and Choose A Way.
We are subsequent up with AMD relating to quite a few of the listings, as it seems that some processors don’t have mitigations however. Also, we’re eager to understand far more about any probable overall performance penalties.